What is custom script extension?
The Custom Script Extension downloads and executes scripts on Azure virtual machines. This extension is useful for post-deployment configuration, software installation, or any other configuration/management task. Scripts can be downloaded from Azure storage or GitHub, or provided to the Azure portal at extension runtime. The Custom Script extension integrates with Azure Resource Manager templates, and can also be run using the Azure CLI, PowerShell, Azure portal, or the Azure Virtual Machine REST API.
This document details on how to use Custom Script Extension using the Azure PowerShell Module against an already provisioned Azure Windows virtual machine to install BigFix client.
Pre-requisites:
Operating System
The Custom Script Extension for Windows can be run on Windows 10 Client, Windows Server 2008 R2, 2012, 2012 R2, and 2016 releases.
Script Location
The script needs to be stored in Azure Blob storage, or any other location accessible through a valid URL.
Internet Connectivity
The Custom Script Extension for Windows requires that the target virtual machine is connected to the internet.
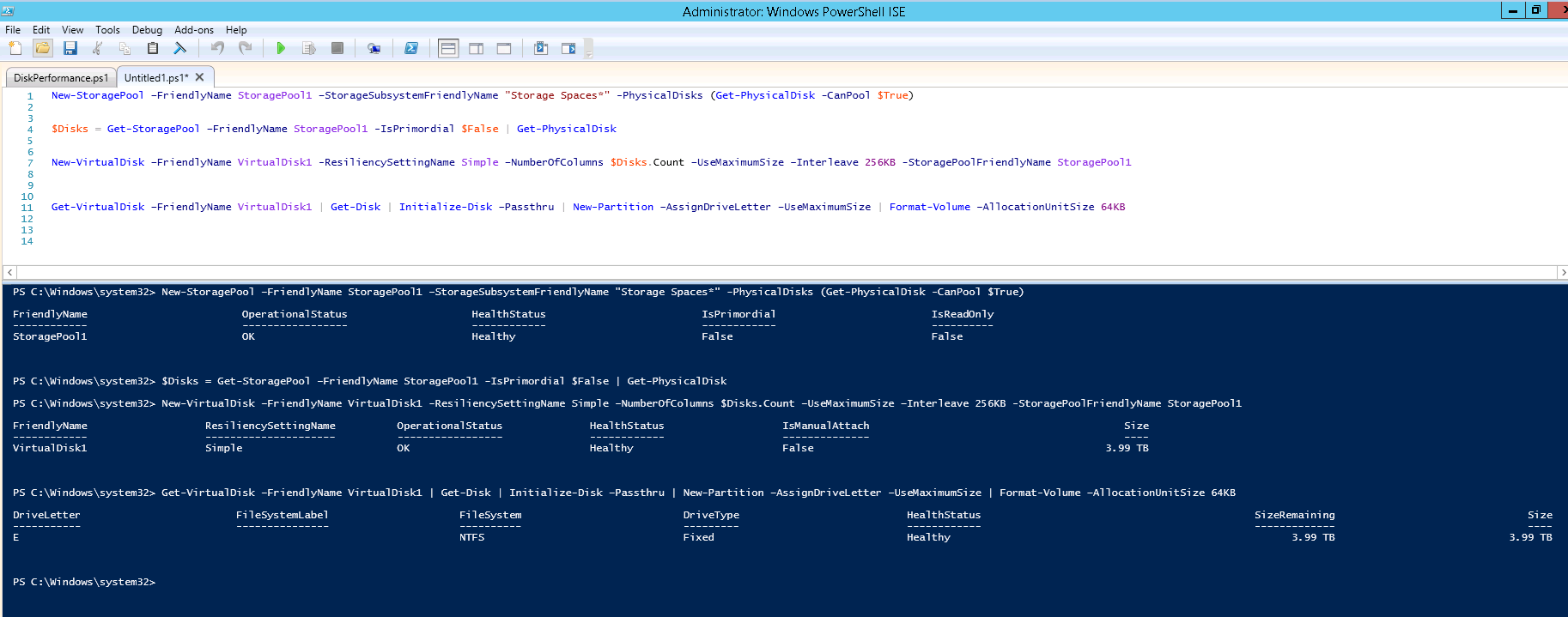
The BigFix client files are stored in the storage account:
![]()

We shall be naming the extension as “bigfixinstallextension.” Make sure that an extension with the same name already does not exist.
Step 1: Get the Azure virtual machine config object
$vm = get-azurermvm -ResourceGroupName “datadog-test” -Name “dg-private-1”
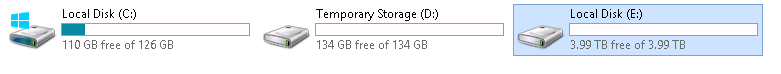
Step 2: Query the Virtual Machine object for existing extensions:
$vm.Extensions
You should see an output similar to below if it does not have any custom extensions.
![]()

Note: any azure virtual machine will have one default extension – “MicrosoftMonitoringAgent.” This is because Azure installs “Microsoft Monitoring Agent” on every virtual machine. Make sure, the virtual machine does not have another extension with the name “ bigfixinstallextension.” If it does have, we have to remove that extension.
Below link provides an Azure Powershell cmdlet to remove the extension:
https://docs.microsoft.com/en-us/powershell/module/azurerm.compute/remove-azurermvmextension?view=azurermps-5.5.0
Once, we have confirmed that a custom extension with name “ bigfixinstallextension” does not exists, we can proceed in adding one. Below is the powershell code:
# Resource group of virtual machine
$resource_group = “datadog-test”
# location of virtual machine
$location = “East US 2”
# azure virtual machine name
$vm_name = “dg-private-1”
# storage account name where the custom script is stored
$storage_account_name = “xxxx”
# storage account key of where the custom script is stored
$storage_account_key = “xxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxx”
# custom script file name
$file_name = “azure_custom_script_execution_install_bigfix.ps1”
# container name where the custom script is stored
$container_name = “msifiles”
# extension name for the custom script extension
$extension_name = “bigfixinstallextension”
# azure powershell cmdlet to execute add the custom script extension and to execute the powershell file
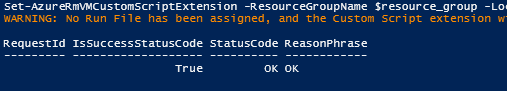
Set-AzureRmVMCustomScriptExtension -ResourceGroupName $resource_group -Location $location -VMName $vm_name -Name $extension_name -TypeHandlerVersion “1.1” -StorageAccountName $storage_account_name -StorageAccountKey $storage_account_key -FileName $file_name -ContainerName $container_name
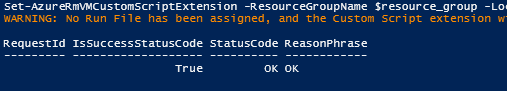
Output:
![]()
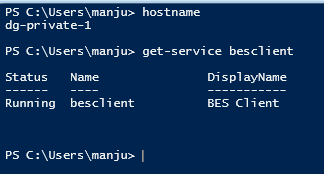
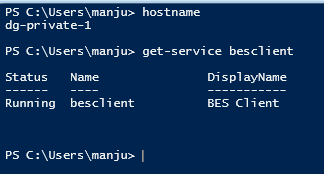
Now login to the Azure windows virtual machine to confirm if the BigFix client is installed and running:
![]()
The downloaded file can be found inside the virtual machine at the below file path:
C:\Packages\Plugins\Microsoft.Compute.CustomScriptExtension\1.9\Downloads\1
Extension execution output is logged to files found under the following directory on the target virtual machine. For troubleshooting.
C:\WindowsAzure\Logs\Plugins\Microsoft.Compute.CustomScriptExtension
Explaining the PowerShell script – azure_custom_script_execution_install_bigfix.ps1
This script gets executed as part of the Custom Script Execution. And it is responsible for installing the BigFix agent.
Below is the code:
# Create a directory to hold BigFix files
new-item ‘c:\bigfix’ -ItemType directory
# Copy BigFix files from Azure storage to local directory
Invoke-WebRequest -Uri https://customsc.blob.core.windows.net/msifiles/clientsettings.cfg -outfile ‘c:\bigfix\clientsettings.cfg’
Invoke-WebRequest -Uri https://customsc.blob.core.windows.net/msifiles/masthead.afxm -outfile ‘c:\bigfix\masthead.afxm’
Invoke-WebRequest -Uri https://customsc.blob.core.windows.net/msifiles/setup.exe -outfile ‘c:\bigfix\setup.exe’
# Execute the setup file
$arguments = “/S /v/qn”
$filepath = “c:\bigfix\setup.exe”
Start-Process $filepath $arguments -wait
Execution Flow:
1. Create a directory to hold big fix files.
2. Copy the three files associated with BigFix installation to the directory created in Step 1.
3. Execute the setup file in silent mode.